دسته: Tools
-
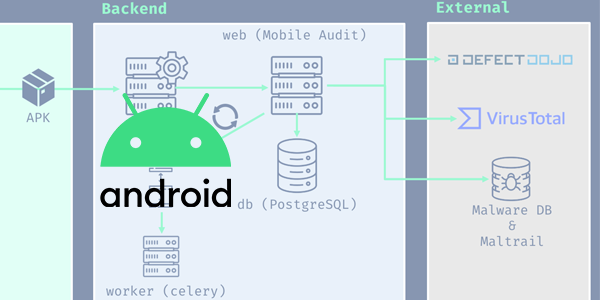
بررسی و آنالیز برنامه اندروید
برای بررسی سریع برنامههای موبایل بخصوص در اندروید روشهای مختلفی وجود دارد. آنالیز استاتیک یا داینامیک برنامههای APK علاوه بر بررسیهای امنیتی و تکنولوژیهای مورد استفاده برنامههای اندروید، میتونه روش سریعی باشه برای پیدا کردن SDKهای استفاده شده در برنامهها، بخصوص برای فعالیتهای بازاریابی و Digital Marketing. من معمولا از این سه سرویس آنلاین برای…
-
theHarvester
theHarvester is a tool for gathering e-mail accounts, user names and hostnames/subdomains from different public sources. It’s a really simple tool, but very effective.
-
SEAT
SEAT (Search Engine Assessment Tool) is the next generation information digging application geared toward the needs of security professionals. SEAT uses information stored in search engine databases, cache repositories, and other public resources to scan a site for potential vulnerabilities. It’s multi-threaded, multi-database, and multi-search-engine capabilities permit easy navigation through vast amounts of information with…
-
tcptraceroute
tcptraceroute is a traceroute implementation using TCP packets. The more traditional traceroute(8) sends out either UDP or ICMP ECHO packets with a TTL of one, and increments the TTL until the destination has been reached. By printing the gateways that generate ICMP time exceeded messages along the way, it is able to determine the path…
-
tctrace
TCtrace is like itrace a traceroute(1) brother – but it uses TCP SYN packets to trace. This makes it possible for you to trace through firewalls if you know one TCP service that is allowed to pass from the outside.
-
protos
Protos is a IP protocol scanner. It goes through all possible IP protocols and uses a negative scan to sort out unsupported protocols which should be reported by the target using ICMP protocol unreachable messages.